SolarWinds Incident Explained: Why User ID and Password Authentication Alone Cannot Prevent Cyberattacks
SolarWinds Incident Explained: Why User ID and Password Authentication Alone Cannot Prevent Cyberattacks
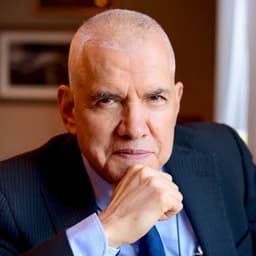
Raul Mendez | President and CEO
International System Research Co., Ltd.
January 22, 2021

In 2020, as the world struggled with the global spread of COVID-19, another new virus quietly infiltrated many systems: Sunburst malware. This incident is one of the largest cyberattacks in history and will bring significant changes to the IT industry.
The catalyst for detecting this cyberattack was when the attackers attempted to log in using a FireEye employee's user ID and password.
In this blog, we'll introduce this cyberattack case study and explain why authentication should be strengthened.
Overview of the Incident: Damage Extended to 18,000 Companies, Including US Government Agencies and Major US Corporations
First, let's summarize the incident based on the blogs of the companies involved in this cyberattack.
FireEye, a leading cybersecurity company specializing in cyberattack detection and incident response, announced in a blog on December 8 that the company had been breached by a nation-state attacker.
Their Red Team diagnostic tools, designed to test security programs against real-world attack scenarios, had been accessed. On December 13, collaboration with FireEye, Microsoft, and SolarWinds published investigation findings in a blog post.
For nine months leading up to the attack's detection, attackers infiltrated the networks of 18,000 companies. This included multiple US government agencies (Justice, State, Treasury, Commerce, and Energy) and major US corporations, transferring data to servers in foreign countries.
On December 17, Microsoft President Brad Smith stated that "this attack has brought a moment of reckoning." He explained that malware was embedded in upgrade files of SolarWinds' "Orion" product, installed by over 17,000 customers.
On January 7, 2021, SolarWinds' new CEO stated that the Sunburst attack is believed to be one of the most complex cyberattacks in history.
Reports to the SEC revealed the attack began with a compromise of Microsoft Office 365 email. Attackers then accessed source code for the Orion product and hijacked servers on the network to spread damage. Investigation revealed that password guessing and spray attacks were used in several cases.
"The best way for attackers to get into your system is to get you to use your ID and password" - How FireEye Inc. discovered the incident
How exactly did FireEye detect this incident?
It was FireEye, not a US government intelligence agency, that detected this cyberattack. If the company hadn't detected the attack, the incident would likely still be ongoing.
Attackers used Sunburst malware to steal employee IDs and passwords. At an online panel event, FireEye CEO Kevin Mandia explained that "the attackers logged into the company's VPN in the same way an employee would typically use it."
FireEye used multi-factor authentication (MFA) requiring a unique code. Because attackers couldn't log in with only credentials, they attempted to register a new device for MFA. This automatically triggered an alert to the security team.
Mandia stated: "Someone registered a device as a second factor and was accessing our network. When we contacted the employee to verify, we found out that the access was not by that person." He realized then that the attackers were highly sophisticated.
So, why is this the "best way" for attackers to intrude?
While major corporations use MFA, traditional password-centric authentication is still common. With the remote work boom in 2020, access restrictions like IP verification were often bypassed for simpler password-only VPN logins. This made "getting users to use IDs and passwords" the path of least resistance for hackers.
How to avoid cyber attacks: Passwordless Authentication and "Authentication Restoration"
The FIDO Alliance was established in 2012 to standardize secure online authentication using biometrics, independent of passwords. Major IT companies like Google and Microsoft have since joined.
ISR joined the FIDO Alliance in 2014. In 2015, we provided Pocket CloudGate, a dedicated application using smartphone biometrics, through CloudGate UNO.
Since 2019, we have provided passwordless authentication using facial recognition and fingerprint authentication via security keys, Windows, and Macbooks.
At ISR, we call the transformation to fast, accurate, and cyberattack-resistant biometric authentication an "Authentication Renaissance." We believe that starting in 2021, triggered by the SolarWinds incident, this passwordless renaissance will spread.
To prevent the expansion of damage from even one more cyberattack, we will strive for an authentication renaissance in Japan.



